Five things to ask before buying a server cluster for edge computing
High-performance compute infrastructure is breaking free from the confines of the data center and moving closer to the rapidly expanding volumes of data at the “edge.” But the environment at the edge can be unforgiving, presenting unique challenges when deploying edge-ready server clusters—rugged systems that can operate in the field with limited space, unreliable power sources and the ever-present exposure to physical security risks. Before building your edge-ready computing platform, ask yourself the following five questions to save time and money, and mitigate risks.
1. What are my performance requirements not only today, but also, tomorrow?
It is important to consider your current and future computing requirements. Edge applications are constantly evolving while maintenance costs are ballooning. This has the potential to dominate your IT budget if not planned for. Buying the latest technology ensures equipment will remain current years after deployment – eliminating the need to “rip and replace” on an ongoing basis. A knowledgeable server manufacturer will help you leverage the latest technology and get the most performance for your IT dollar.
Also, remember that serviceability and upgradeability are vital for edge systems. Modular blade servers are an ideal fit for fast-evolving compute requirements since they allow architectures to evolve incrementally. These servers also eliminate the need for complete system replacement, lowering cost of ownership with easily upgradeable individual lightweight blades.
2. Where am I operating?
Edge servers can be deployed in a wide range of settings and platforms, including farms, oil fields, factories, naval surface and submarine vessels, aircraft, and armored vehicles on the battlefield. In every location, edge-ready servers must be rugged and secure, delivering unhindered, reliable functionality over their expected lifespans. Environmental considerations should include operating in extreme temperatures, humidity, shock, vibration, sand, salt and dust. And because many mission-critical applications require that computing infrastructure be tested and certified to rigorous standards, edge-ready systems must be designed to survive in these unique field environments. Failure to perform can result in significant business losses or mission failure. Each edge application is unique. Make sure you work with an experienced partner with a successful track record of designing and testing systems for edge deployment.
TIP: Ask your rugged server manufacturer if they have designed systems for field-proven standards such as MIL-STD, MIL-DTL, IEC, DO-160, EN 50155 and TEMPEST
3. What are my space and power limitations?
Edge deployments are often constrained by available space and limited power. Servers specifically designed for the edge are optimized for transport and deployment in small spaces. Transit cases and small form-factor housings can simplify logistics for mobile computing applications, while flexible AC/DC power supplies allow equipment to operate in areas inaccessible to standard server power sources found in the data center.
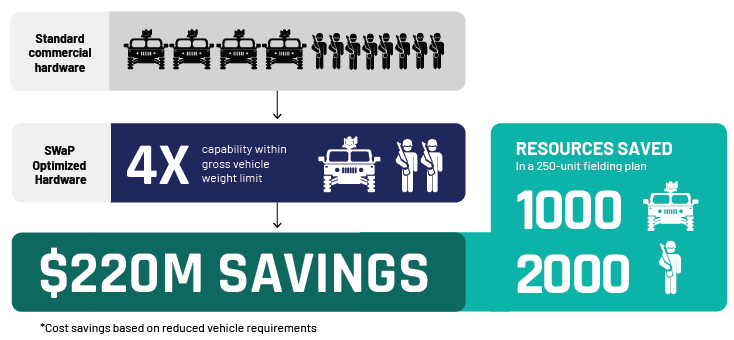
Optimizing for size, weight and power (SWaP) is a complicated game of trade-offs. When choosing SWaP-optimized servers, consider partnering with an experienced provider with the requisite thermal, kinetic and mechanical expertise.
4. Will my confidential or sensitive data be safe?
At the edge, secure premises may not be available and software-level cybersecurity measures can be insufficient to secure hardware containing sensitive information. Systems exposed in the field are subject to attack, offering an adversary the opportunity to extract sensitive data or reverse engineer critical system details. While securing a data center may be as easy as locking a building, protecting servers in the field from theft, loss or compromise is far more difficult. Built-in secure boot, secure processing and physical protection technologies can offer design protection and cyber resiliency to maintain system-wide confidentiality and integrity.
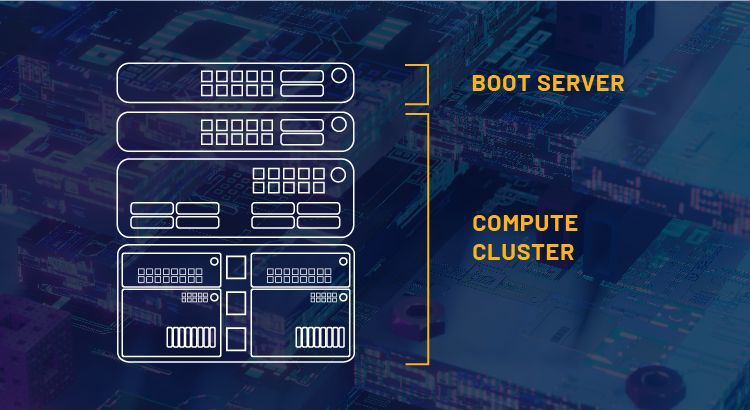
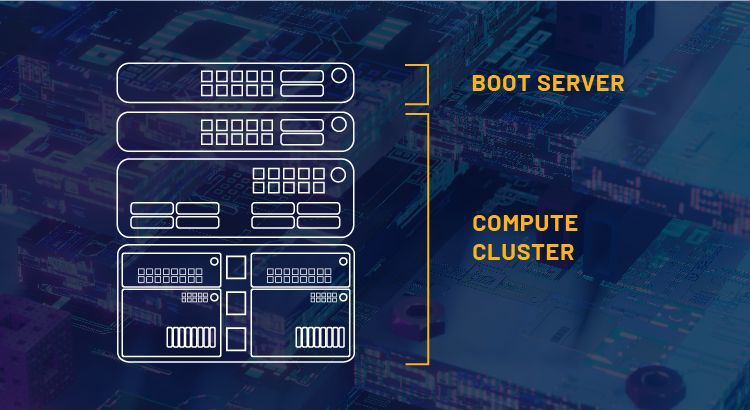
Ask your server supplier if they can help you deploy a secure boot server as part of your edge-ready cluster. This specialized server has built-in security that protects against unauthorized modification of your cluster configuration or software stack. It maintains data integrity even when offline or remotely accessed. System security exists on a spectrum; each application must tailor security needs to mitigate the risk and cost of compromise.
5. How does my server stack fit into my existing IT ecosystem?
Rugged servers featuring commercial-off-the-shelf (COTS) components and technologies, like Intel® Xeon® Scalable processors, are affordable and easier to integrate than proprietary edge computers because they are pre-certified to run a range of software and applications out of the box. They seamlessly plug into existing IT infrastructure, simplifying management across cloud and edge layers, and can be quickly deployed. While rugged servers designed and built with proprietary or custom components do not deliver these capabilities, they may deliver security advantages. Working with a rugged-server expert with experience in both design approaches will allow you to explore the trade-offs and understand the costs and benefits of both.
The challenge is to build an edge computing infrastructure that delivers data-center performance in a rugged, compact and secure design. Mercury’s server experts are ready to help architect a rugged server cluster that works for you – contact us today.
• Watch Video: Servers Built for Every Inhospitable Corner of the Globe
• View Product Offering: Rugged Edge Servers








 Women leaders at Mercury: Cultivating hope. Building confidence. Raising optimism.
Women leaders at Mercury: Cultivating hope. Building confidence. Raising optimism. Empowering female leadership: A conversation with Mercury’s CMO, Stephanie Georges, and SVP Dr. Amela Wilson about resilience and authenticity
Empowering female leadership: A conversation with Mercury’s CMO, Stephanie Georges, and SVP Dr. Amela Wilson about resilience and authenticity