
Sailing Through the Fog into the Edge
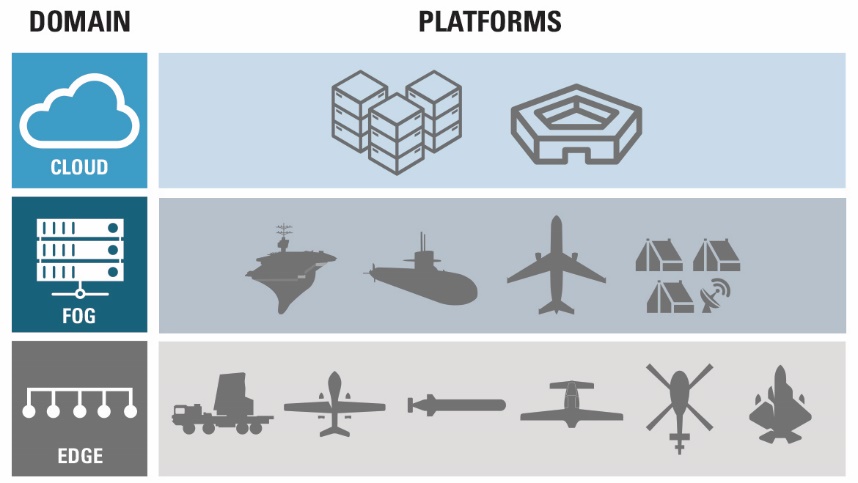
Cloud, Fog and Edge Computing for Defense Applications
More or Less the Same Cloud
Confined to fixed sites, commercial cloud-computing servers are scalable, cost-optimized systems with abundant storage, high processing power, and low latency I/O. With plenty of space, air conditioning and reliable electrical power provided through the grid and backup generators, these systems don’t typically need to be environmentally resilient.
Although cyber security does cut across all layers (edge, fog and cloud), cloud facilities can provide higher levels of on-site physical and personnel security to prevent tampering or reverse engineering, somewhat reducing the requirements on tamper-proof hardware. However, there are some unique demands on defense cloud computing solutions versus their commercial counterparts, such as added security requirements and slower upgrade rates that impact technology sustainment.
One high-profile example is the Pentagon, who will soon move towards a commercial ‘secure’ cloud system to maximize capabilities and store classified data.
Sailing Through the Fog
Located between the cloud and edge layers, fog computing reduces the cloud workload by providing distributed computing, storage, and networking. Fog systems perform data analytics and data reduction to improve response times back to devices that cannot be at the edge due to mobility restrictions.
For defense applications, fog computing may be thought of as mobile micro-data centers. A Naval destroyer, for example, contains hundreds of fog computing elements that carry out functions ranging from target acquisition, tracking, fire control, communications, sensor fusion and battle management. Fog computing facilitates communication and collaboration between “nodes”, such as Unmanned Underwater Vehicles (UUVs) or sensor buoys, in the edge layer.
In the defense domain, fog-computing requirements are shaped by factors such as:
- Greater latency: Outdated networking caused by large time gaps between hardware purchase and deployment.
- Restricted cloud connectivity: In part caused by closed systems and nation-state level security concerns.
- Platform mobility: On the move platforms require processing resources with protection from shock, vibration, and wide temperature fluctuations.
- Unknown adversaries: Increasing the need for security and fast response, adaptive systems.
Defense fog layer processing resource features include:
- Redundancy and reliability: To ensure uptime of key systems in all environments.
- Reduced size, weight, and power (SWaP): To pack more compute power into the same volume and reduce consumed power.
- Higher performance: Sometimes even higher performance than fog systems found in the commercial world due to closed defense systems and restricted cloud links. Sending data to and from the cloud for analytics processing and response actions can be inefficient for latency sensitive applications.
- Deploying the latest technology: To counter new adversary technology developments.
- Security: While the commercial marketplace has privacy concerns, leakage of or tampering with sensitive data in the defense domain can compromise missions and/or lead to national security concerns.
To meet this expanding range of requirements, our EnterpriseSeries servers feature over 50 form-factors that can be configured to meet a variety of performance, security, and reliability needs. By collaborating with component technology leaders, like Intel, we align technology roadmaps with product designs and defense customer deployment timeframes. This allows us to ensure technology solutions remain available for current and future deployments. For example, newer Intel processors are available for 15 years, providing the foundation for long-life, standards-based, network-ready solutions for defense applications, backed by Intel’s 30+ years of experience in delivering world-class computing and communications solutions.
5G networks, which have been touted to overcome current communication liabilities and restrictions, will require robust and secure fog computing to deliver on all of the promised benefits. Their proximity to the edge significantly reduces service response times and improves QoS/QoE levels, resulting in a superior user experience. These benefits are not limited to commercial users, as U.S. military forces are poised to leverage 5G to improve connectivity, provide massive bandwidth for advanced analytics, empower mobile mission capabilities, increase situational awareness and enhance real-time mission command capabilities, just for starters.
Flying into the Edge
The Internet of Things (IoT) is not confined to the commercial world. The proliferation of sensors, data and new technology is driving the need to migrate computing power from the data center, across the fog layer, and into an increasing number of defense edge applications. Defense applications deployed at the tactical edge, such as smart autonomous vehicles, cognitive radars and smart sensors, necessitate edge computing systems to perform mission critical analytics and real-time processing at the site of deployment.
Consider an unmanned aerial vehicle (UAV) that communicates with a fog infrastructure and performs sensor (EO/IR, radar, LIDAR) processing and fusion, and PNT computation to execute its mission. The processing power required to perform these operations has to be simultaneously powerful, small, light, and reliable.
Key trends that are shaping edge layer compute resources include:
- Mobility: Higher levels of size, weight and power efficiency for mobility and mission endurance.
- Reliability: Processing resources need to be extremely rugged for deployment in harsh and demanding defense applications. Redundancy is also important to avoid single points of failure.
- Powerful: Autonomous missions require real-time responses derived from huge torrents of sensor data with massive on-platform processing power.
- Processing density: By “doing more” at the edge, bandwidth and security issues associated with data transmission to the cloud are minimized and responses become real-time. Response time can determine mission failure or success.
- Security: Cyber-security threats due to widespread mobile use and a vast, increased number of physically remote devices that can be exploited to gain access to the network.
- Safety: When lives are at stake, safety is of utmost importance. The exponential increase in distributed, powerful, and potentially destructive platforms in the field directly impacts the requirement for embedded safety capabilities.
Meeting these trends requires:
- SWaP: Engineering the latest electronic packaging, miniaturization, cooling and power management technologies to maximize compute density and increase reliability.
- Ruggedized hardware: Developing and applying advanced design and manufacturing techniques at the component, board, assembly and box level assures performance under extreme environmental conditions.
- Embedded processing: Embedding the most contemporary high compute, low-latency technology such as FPGAs, GPUs, and Intel® Xeon® Scalable processors.
- Built-in security: Building in system security engineering and cyber resilience for holistic system integrity.
- Certifiable safety: Designing the highest level of hardware and software flight-safety design assurance for platform avionics and vetronics.
Mercury’s pre-engineered building blocks based on the industry-leading processors from Intel® enable powerful, rugged, trusted, safe and secure processing resources to be embedded into edge defense applications. Enabled with flight safety certification for critical effector operation, these processing subsystems can be deployed in civilian aerospace and on public roads as well as in the most contested, remote and harsh military environments.
Expertise is Key
To successfully design, develop, and deploy the latest and most relevant technology platforms at increasingly shorter cycles, significant engineering investment combined with proven expertise is essential. Due to logistics and government processes, upgradeability is an issue for both Fog and Edge Computing systems. To simplify technology refresh, open system architectures, modularity, composability, and extensibility need to be built-in at the design level. This ensures long-term sustainability, reduces the total cost of ownership, and streamlines deployment.
Stay tuned for our next post where we'll explore these fog and edge computing trends and their enabling #IoT technologies as they apply to both defense and commercial domains.
This post was written by Shaza Khan, Laura Hanks, and John Bratton. @IntelIoT





 RDS and Future Vertical Lift: Putting a data center in the sky
RDS and Future Vertical Lift: Putting a data center in the sky Top 10 Highlights of 2021
Top 10 Highlights of 2021