Protect Classified and Sensitive Information with Military-Grade Encryption
Data deployed at the edge and in critical systems must be protected from local or remote attacks. Field-proven and certified encryption modules demonstrate how the Mercury Processing Platform supports mission-ready, trusted solutions utilizing our core security technologies, which safeguard information and meet government mandate requirements.
Protect Data and Deploy Anywhere
Secure
NSA Type-1, FIPS 140-2, CSfC
Compact
Low size, weight and power (SWaP)
Rugged
MIL-STD 810/461, DO-160
Easy to Integrate
Embedded and tailored systems
Thank you! We have received your message and will be in touch with you shortly.
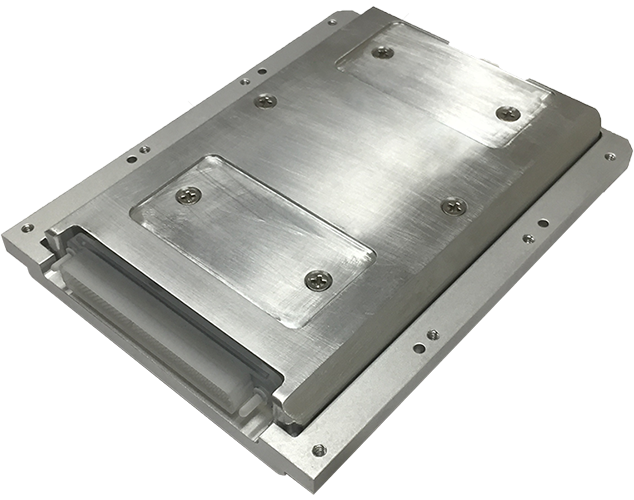
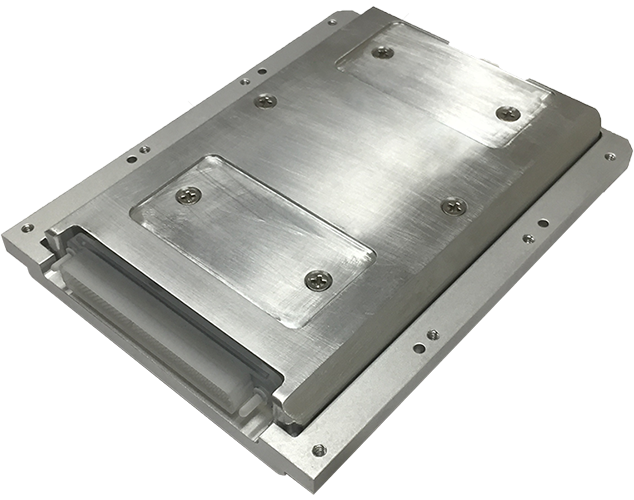
FEATURED PRODUCT
JDAR NSA Type-1 Data-at-Rest Encryption Module
A small, 0.9 lb, rugged, NSA-certified Type-1 data-at-rest encryption module for embedded VPX/VNX, rackmount, or custom systems that protects Secret and Below (SAB) data and can be left unattended.
Featured

Blog
This is not a drill: Preparing for a severe cyber stormDesigning post-quantum cryptography (PQC) is much more than just implementing an algorithm. You need ...
Angie Giles
September 19, 2022
Read More
Blog
Can you trust your computer? Three ways your system may already be unsafeShaza Khan
March 21, 2022

Vodcast
Solving security, integration and system performance challenges for today’s – and tomorrow’s – Air ForceMercury Systems
March 10, 2022
BUILTSECURE SOLUTIONS
Protect Your Critical Data and IP
Solutions with BuiltSECURE™ technology maintain your data integrity with built-in cryptography, secure boot and physical protection technologies that have been developed over 25 years and proven across four generations of Intel® microarchitectures.