Protecting sensitive data and system integrity is imperative to mission success.
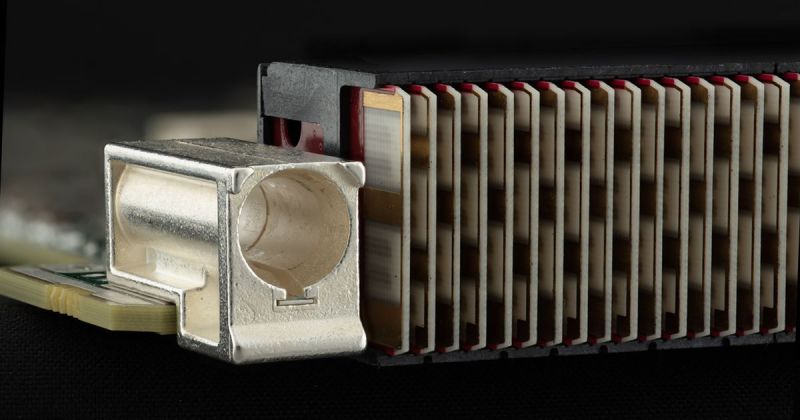
The SecRun security platform utilizes a combination of proven, secure IP technologies to counteract threats.
An advanced cryptography solution for ASIC and FPGA designs, SecRun minimizes the likelihood of accidental misuse or coding errors that can expose sensitive cryptographic keys during system boot and runtime.
SecRun combines SecBoot, InCipher and KeyGuard technologies to defend against side-channel attacks (SCA), prevent key leakage, store and guide keys at boot and runtime and perform automatic key refreshes to ensure all critical system information is protected and secure.
Protection Customizable to Fit Any Application
Integrate the SecRun security platform with SecBoot, InCipher and KeyGuard as a standalone capability into any existing FPGA and ASIC-based system or as part of a bundle on supporting embedded processing hardware.
- SecBoot securely initializes memory devices from an external NVM in ASIC systems and deploys SCA countermeasures during device start-up in FPGA-based systems, ensuring no leakage of sensitive information even when exposed to the most aggressive cyber threats.
- InCipher provides transparent encryption of DDR memory while implementing caching and best practices for key management. Using automatic and transparent re-keying during operation and highly effective SCA-resistance options, the risk of adversaries acquiring sensitive information is eliminated.
- KeyGuard, already prepared for use with SCA-resistant ciphers, securely manages storage to protect keys at rest and performs key-agreement protocols to establish new keys directly within the key manager.
- PQ Ultra protects ASIC and FPGA applications against quantum-computer threats, implementing the new quantum-computer resistant algorithms recently finalized by the National Institute of Standards and Technology (NIST).
Thank you! We have received your message and will be in touch with you shortly.
Explore Mercury Hardware Supporting SecRun
OpenVPX Embedded Processing
Pre-integrated, SWaP-optimized, customizable OpenVPX multifunction subsystems with program support services, security.

Rugged Trusted BuiltSECURE Servers
Reliable and trusted, enterprise-class performance for the most security-imperative mission-critical applications
Multiprocessing
6U OpenVPX multifunction boards powered by server-class Intel Xeon Scalable processing technology
Single Board Computers
Feature the latest Silicon Valley processing technology and next-generation flight-certifiable multicore processors
FPGA Boards
Speed your high-performance processing application with rugged COTS FPGA boards
PURPOSE-BUILT SECURITY
Your Technology, Protected
When you work with Mercury’s engineers, your sensitive information and technology are protected through best-in-class security technology and field-proven methodologies and practices.

